DAG Definition: What is a DAG (Directed Acyclic Graph) in Crypto?

What is a DAG?
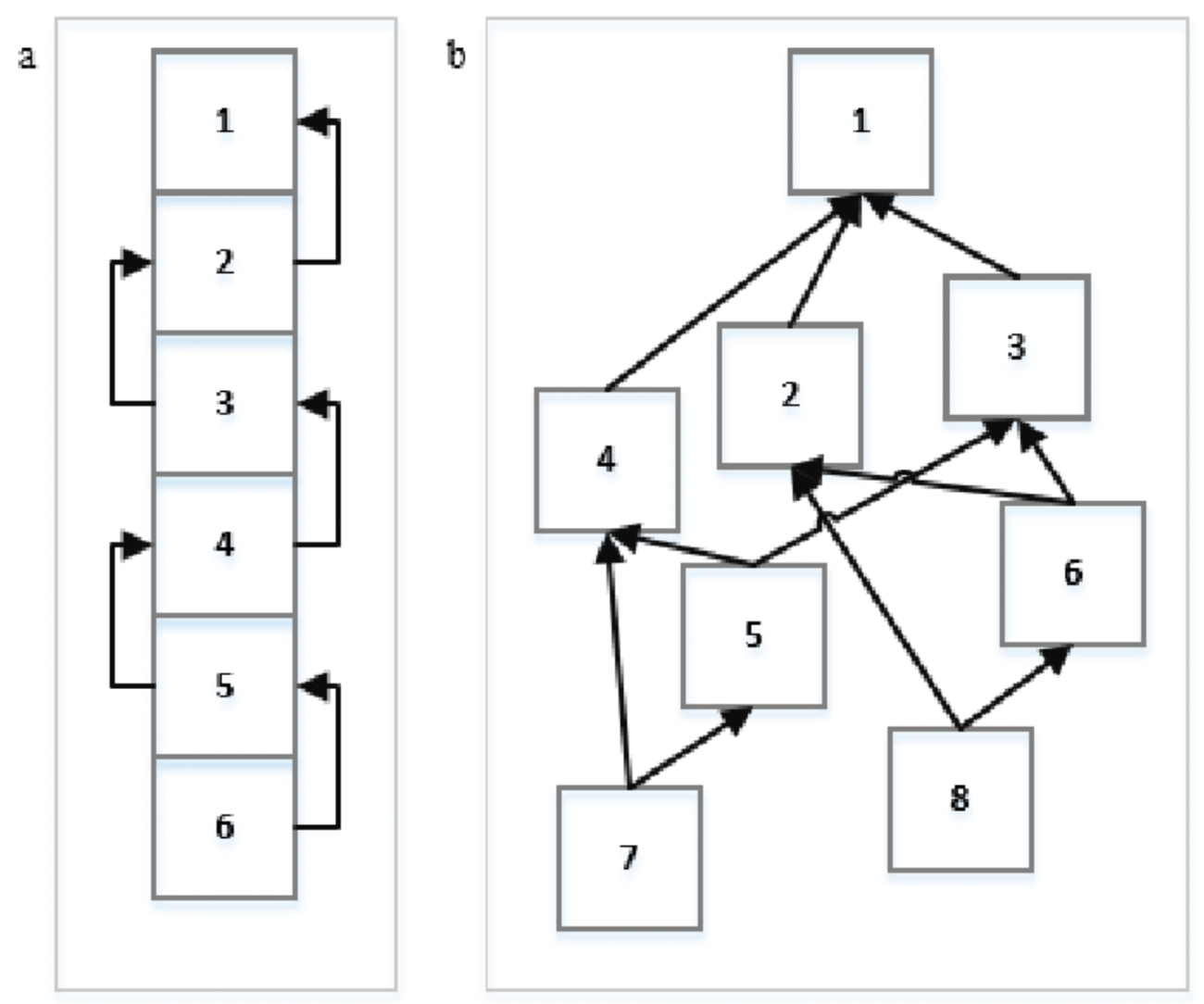
A DAG (directed acyclic graph) is a particular kind of data organizing tool that links numerous bits of data together. In contrast to a blockchain, which consists of blocks, directed acyclic networks have vertices and edges. As a result, cryptocurrency transactions are listed as vertices. These transactions are then combined with one another in the recording.
However, the method DAG receives transactions from nodes is similar to how a blockchain works. Nodes must complete proof-of-work (PoW) tasks to complete a transaction.
A blockchain system does look like a chain, whereas a DAG system appears more like a graph. Because it is effective at processing online transactions and storing data, the DAG model is now thought of as a potential replacement for blockchains in the future.
The DAG model is a potential remedy for the present decentralization problem in crypto. This strategy eliminates the need for miners to compete for new blocks to add to the chain.
Transactions can also be processed more quickly when nodes are built concurrently. The usability of a network can be enhanced if it is more scalable, and developers are looking at DAG as a better, more secure alternative.
How does DAG work?
The directed acyclic graph model stores data more effectively than other current methods. With connected nodes acting as its "branches," it has a tree-like structure.
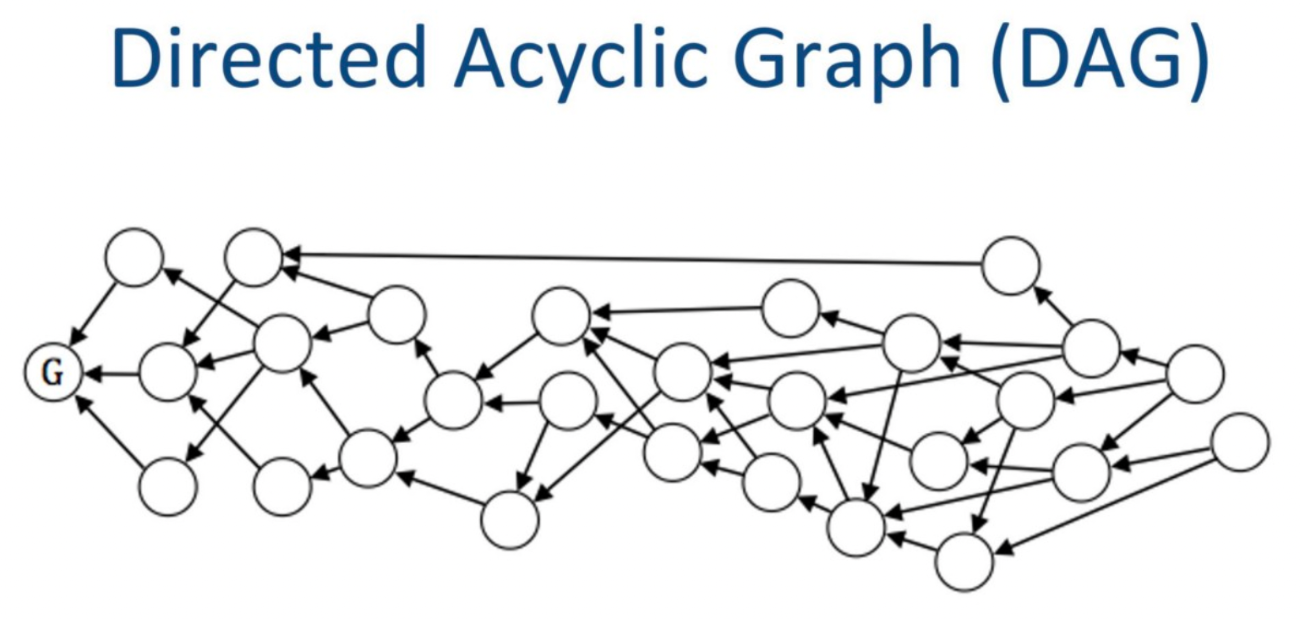
Because each node may have multiple parent roots, the paradigm allows for more transactions to be validated concurrently. Users do not need to wait for previous transactions to complete in order to process new ones.
In a directed acyclic graph, for a new transaction to be approved by the network, it must be related to previous transactions. Blockchain blocks also make references to older blocks in the same way. This is supported by the fact that a transaction can only be correctly confirmed when it references another transaction and so on.
A transaction is represented by each vertex in a DAG. Additionally, since there are no blocks, mining is not required. Transactions are built upon one another rather than being put into blocks. When a node submits a transaction, proof-of-work activities are then carried out to verify prior transactions and avoid spam, as already mentioned.
New transactions are often added on top of older ones in a DAG-based cryptocurrency. A DAG and a blockchain are fundamentally different from one another in that multiple transactions can be referenced at once as opposed to only one.
Some programs employ an algorithm that selects transactions or "tips" in accordance with weighted averages (or the number of confirmations leading up to the tip).
When nodes confirm prior transactions in DAGs by analyzing a path that can be traced back to the DAG's start transaction, double-spend protection is enabled. This confirms the sender's balance is sufficient. If users construct on the wrong path, their transactions could be refused.
Conflicts created by different courses are resolved via a selection technique that favors suggestions with a higher cumulative weight.
DAG Examples
The DAG architecture has several limitations in terms of smart contract functionality and permissions issues, but it is highly effective at processing and storing data.
DAG has a fairly limited variety of applications as a result, and the technology is still in its early stages.
Obyte, IOTA, and Nano are a few instances, just to name a few. Even though the DAG structure is still rather new, it has a lot of potentials. It has previously been successfully used in a number of projects, as was already mentioned. The most well-known are:
IOTA
IOTA, which focuses on Internet of Things applications, developed DAG architecture to make transaction processing considerably quicker and less expensive than it was with 2016's blockchain architectures. (97421) The idea behind IOTA is that every user that joins the network effectively turns into a "validator."

Nano
Nano is a cryptocurrency that utilizes a hybrid DAG/Blockchain technology. Block-lattice is a method whereby nodes connect separate blockchains in nano.
Each user in Nano has a unique Blockchain and wallet. Changes to a user's wallet or blockchain are only possible by users. A transaction is complete when the sender and the receiver change their respective blockchains.

Obyte
Obyte, sometimes known as ByteBall, is a cryptocurrency that uses the DAG framework and is entirely independent of the blockchain. However, there is still a charge for Obyte transfers.
Transactions may be double-checked thanks to the validator system used by the Obyte network. It employs a consensus mechanism that is dependent on eyewitnesses. These witnesses serve as validators and are regarded as reliable users.
Obyte supports both unreachable contracts and untraceable transactions.
Pros and Cons of DAG
Pros
Transaction speed: Transactions can be sent and processed at any time, not just during blocktime. A user can send an unlimited number of transactions, provided they simultaneously confirm the older ones.
Low Energy: Unlike conventional blockchains, DAG does not employ the well-known PoW or POS consensus algorithms. As a result, they have substantially lower operational expenses and a far smaller carbon footprint than cryptocurrencies that rely on PoW blockchains.
No transaction fees: In a pure DAG design, users pay no fees or minimal transaction processing costs. This is appropriate for tiny transactions with little value.
Scalability: DAGs may handle more transactions per second than conventional blockchain networks since they are not constrained by blocktime. This, according to many supporters, will make them useful in the Internet of Things (IoT) application cases.
Cons
Not completely decentralized: Using the DAG design means that some aspects of centralization will still be present in protocols. This restriction can be significant for certain people.
Attack via spam: Because DAG systems have almost no transaction fees, malicious users can easily send spam throughout the network.
FAQs about Directed Acyclic Graph
What are the purposes of DAG?
Although there is still room for improvement, DAG can be considered a competitive alternative to blockchain. Regarding cost, performance, and scalability, the DAG architecture aims to address significant problems with blockchain technology.
The two methods technically accomplish the same by recording transactions on a digital ledger. The primary difference between the two models is how they keep their data.
Is DAG important for crypto?
DAGs can effectively represent various flows, including data processing operations. One can better organize the many phases and the corresponding sequence for these jobs by thinking of large-scale processing processes in terms of DAGs. The data is often subjected to several computations in different data processing settings to prepare it for one or more final destinations.
Is DAG still in use in the crypto market?
The application of DAGs in cryptography is still in its infancy. They are still not entirely decentralized, in contrast to blockchains. As a result, they are currently more commonly employed to launch networks than to establish a reliable network.